Areas to Mitigate Third-party Risk With Your Procurement Solution

For years, managing third parties’ risks has been a difficult task for businesses of all sizes across all industries. The COVID-19 pandemic has caused a paradigm change from “just in time” procurement and inventory management optimization tactics to “just in case” approaches, increasing pressure and urgency on managing third-party and supply chain disruptions. This can be offset by advanced procurement software that lets you handle disruptions smoothly.
A Deloitte 2020 survey results show that while organisations had to deal with vendor risk management issues before the outbreak of COVID-19, there is now a higher awareness of these issues and a better understanding of the serious consequences of severe third-party failures and how quickly they can cause damage. And then we have the Ukraine-Russia war that clearly shows that mitigating third-party risks is now a critical part of your supply chain.
Three Areas to Mitigate Third-Party Risks with a Good Procurement Software
- Risk Management for Vendors through Procurement Solutions
Third-party risk management is a vital component of any organisation. You may acquire additional insight into the well-being of your vendor population by building a solid foundation with proper planning for each stage of the vendor lifecycle.
Source: Gartner
The following are the basic steps in the vendor risk management process:
STEP 1: Choose your suppliers and create an inventory
STEP 2: Establish your organisation’s risk tolerance
STEP 3: Determine inherent risk and classifications in step three.
STEP 4: Create evaluation questionnaires
STEP 5: Establish a schedule for assessments
STEP 6: Determine who controls the process in step 6
STEP 7: Describe a backup plan in case something goes wrong.
Develop comprehensive, repeatable processes at each stage in collaboration with your team. You’ll be able to proactively manage your third-party risks if you have an end-to-end strategy and an e-procurement solution in place.
- Ongoing Vendor Monitoring: E-Procurement Software Can Help
Ongoing vendor monitoring is arguably the most significant component of the third-party risk lifecycle. Since it lasts the entire partnership, this stage is also the longest. The goal of continuous monitoring is to check your vendor’s security routinely. It will assist you in ensuring your vendor population’s dependability, honesty, and security.
Important risk areas to keep an eye on include:
- Acquisitions & Mergers
- Regulatory adjustments
- Ratings for cybersecurity and financial health
- Changes in business processes
- Sustainability (ESG)
It’s crucial to remember that not every vendor requires the same level and frequency of monitoring of these areas. Assign vendors to criticality tiers and make appropriate assessments to make the process more effective for your team and your vendors. For instance, a vendor in the “high risk” tier needs to undergo more thorough evaluations than a vendor in the “low risk” tier. The vendor monitoring gets easier if you consolidate information about each of them in an e- procurement software and apply it for risk analysis.
- Cybersecurity: Start Using a Good Procurement Software
Organisations now face significant cybersecurity risks from their vendors. Hacking organisations are increasingly focusing on third parties within an organisation as a “back door” to their more difficult-to-crack systems. 51 percent of firms have experienced a third-party-caused data breach, with 44 percent experiencing one in the past 12 months, according to a Ponemon Institute survey. 74% of the 44% of the firms had data breaches as a result of granting third parties an excessive amount of access.
To increase safety in their policies, procedures, and controls, organisations should assess the following cybersecurity risk categories with their third parties:
- Compliance threats: Depending on their services or location, your third-party vendors may have different compliance standards than your company. Learn about the laws and standards that apply to your third parties, and then be aware of the procedures for compliance. Compliance management becomes more effortless with procurement solutions that are needle-casted to your business model.
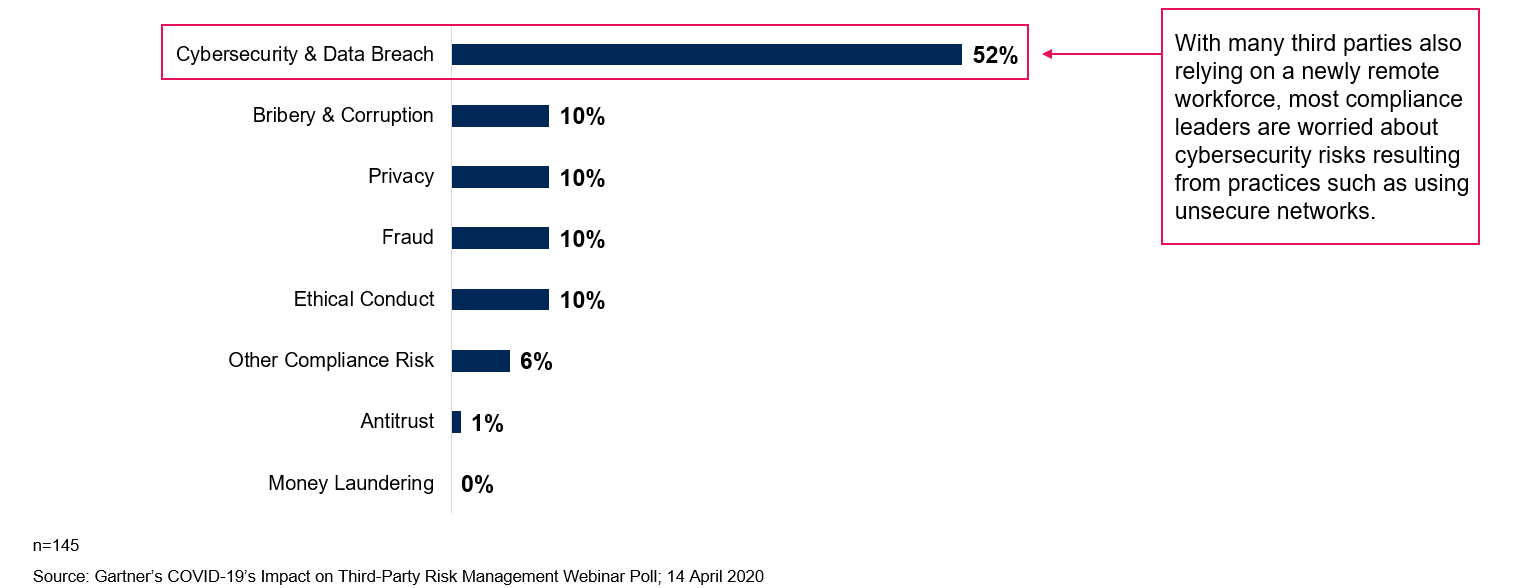
__Source: __ Gartner
2. Operational Risks: Your company may depend on outside partners to offer services crucial to your IT infrastructure or everyday business operations. Recognize the safeguards put in place by third parties to ensure the secure operation of various elements of your business. Ensure that the third party has sufficient procedures to fix any weaknesses in their IT infrastructure.
3. Information Security Risks: Third parties must have measures in place to protect data, whether they are managing sensitive information from your organisation or their own. Make sure you understand every phase of your extremely sensitive data lifecycle as it relates to third parties. Establish the duration of storage of this data by the third parties, ensuring that they are legally obligated to delete it once your business connection is over.
Consider cybersecurity as a platform for communication between your company and its suppliers. Use continual vendor monitoring to promote discussion about cyber risk throughout the partnership.
The Risk from Third Parties Extends Beyond the Supplier/Vendor
When we think about risk, we frequently think of supplier or supply chain risk, but the third-party risk goes much further than that. Any failure inside a company’s ecosystem, whether from the supplier, distributor, support services provider, sales or marketing agent, or any linked bodies, subsidiaries, or joint ventures, could have a dangerous cascading effect on the entire ecosystem.
Hardcore procurement professionals and risk-focused individuals in the sector today perceive risk differently, even though the latter group typically works within the procurement organization. Basically, those who work in procurement rely on procurement software and have a tactical understanding of risk, whereas risk professionals typically have a much more strategic outlook. The CPO, like them, must adopt that strategic perspective, which necessitates factoring in risk before the sourcing process begins.
Procol as Your Risk-Mitigating Procurement Solution
By facilitating frictionless interactions between thousands of buyers and suppliers throughout the whole source-to-contract process, Procol’s procurement solution supports the marketplace for modern business. With an open technology platform, our market-leading solutions help businesses extend their collaborative business processes, mitigate risks, make better decisions, and collaborate with their suppliers. Schedule a Demo!
Get a Free Demo
We'd love to hear from you. Please fill out this form to schedule a demo with us. You can also give a call on +91 76666 82222



